Library Borrowing System Documentation | Chapter III – Methodology
In this article, we will discuss Chapter 3 which is the methodology you used in your thesis. Chapter 3 is focused on the SDLC you used in completing your system.
Here are the steps in writing Chapter 3 Methodology.
How to write Chapter 3 Methodology.
- Methodology
In this section, you will write a short generalization of the whole Chapter 3 and introduce the methodology you used for the system.
- Systems Development Life Cycle (SDLC)
Next is to explain the SDLC used in this system (with diagram). For this Library Borrowing System example, the researchers chose the Waterfall SDLC.
- Discuss the Steps of the SDLC
You need to discuss the steps used in the chosen SDLC. These steps might differ from various SDLC’s.
- Constraints
Next is to enumerate and explain the possible constraints that you might encounter during the development.
- Architectural Diagram
The Architectural Diagram illustrates the connections between the hardware of your system. Also, write a short description below the diagram.
- System Testing and Implementation
In this part of the documentation, you will describe how your system is implemented and tested by the users.
- System Features
In this part of Chapter 3, you enumerate the functions of your system.
- Recommended Hardware Specifications
Next is to list the hardware needed for your system.
- Recommended Software Specifications
Also, list down the applications needed by the system.
- Recommended Network Specifications
Lastly enumerate the network specifications in order for the system to run.
Now that you know the contents of chapter 3, here is the example of the Chapter 3 Methodology of Library Borrowing System .
Chapter 3 Methodology – Library Borrowing System
Methodology
This chapter begins on the scrutiny about the project research design methodology together with the development of the system operation, process and testing.
The second part discussed the architectural diagram interface of hardware and the last part showed the recommended hardware, software and network specification.
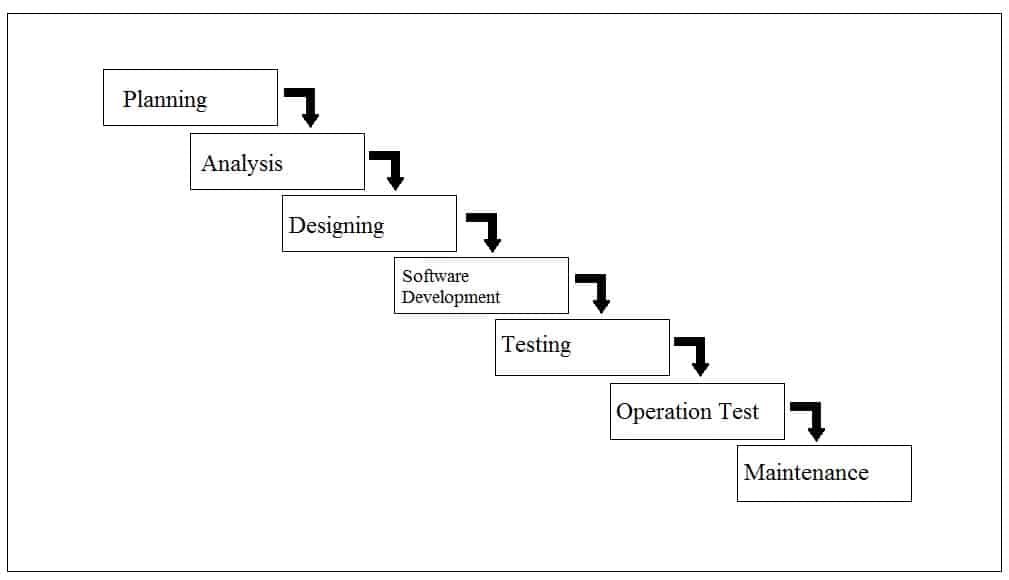
Throughout the project development after the researchers conducted interviews and research regarding the proposed system, the researchers have decided to use Waterfall Model for the System Development Life Cycle (SDLC), because this model gave the researchers lot of advantage including; in each stage and activity done in development of the project those stages and activities were easily explained which benefit both the researchers and the client and also in each verification and review of each stage can easily locate and repair errors that may occur in the program.
Planning
During planning phase of the system, the researchers conducted an interview to the client to gather some data about on how the librarian manage the books, borrowed book records, returned book records, all student’s records in the library.
It is observed that the librarian manually writes all the transactions and maintenance records of every student who borrowed or returned the books in a piece of paper, so the researchers plan on developing the management by improving the managing of records by making it computerized to make it more effortless to both the librarian and clients of the library in the future.
The researchers also plan to provide a more secure and a large amount of database storage for their records to be safe.
Analysis
The proposed computerized Library Borrowing System was designed purely from the users’ viewpoint without considering the restraint of hardware (such as computers hardware and software). In addition, system frameworks required to attain such designs was clarified.
After checking requirement specifications included in the basic plan, the overview of the project was represented through the use of diagrams (Figures: 3-5) so that the alternation and flows of data can be easily assumed.
Designing
The software design particularly designed to the librarian of the school, the researchers used a user-friendly design to attract the user to use the new library borrowing system.
Here, the system was arranged and constructed purely from the users’ aspect without considering the constraints of hardware (such as computers). In inclusion, system structures enforced to achieve such designs were clarified.
After checking the requirement stipulation included in the planning, the synopsis of the system represented by the use of diagrams so that the processed of data can be easily presumed.
Based on the likeness and the division into sub-systems and input/output plotting was performed. The entire project was branched into a number of modules on a utilitarian basis, and each module was further divided into smaller entity.
In designing of the code, such as the boldness of coding system, was conducted. In addition, relationships between the data were analyzed.
Software Development
Coding
In the development of the system, the researchers made use of Microsoft Visual Basic Studio 2008 for encoding the source code of the system, the researchers also made a module for loading of data in each specified field in the system, in order to be accurate and fast acquisition of data and information.
Testing
After finishing the main parts of transaction being done in the system the researchers tested it and there was a lot of learning that the researchers encountered, it made the researchers realized minor and major mistakes in the system and it gave more understanding on how to develop it, after several weeks, the system has been successfully introduced.
Operation
In the operation test, the researchers conducted a test of our system with our fellow BSIT-III students in order to verify and secure the system will satisfy the clients. The researchers received comments and suggestions for consideration.
Maintenance
Maintenance will be conducted once the system is deployed to our clients, to maintain good performance all throughout the school year, maintenance will be done if the clients make a request. The researchers will also conduct a yearly maintenance to ensure their satisfaction.
Constraints
The following were the constraints the researchers had encountered during the gathering of information and making of the system:
Insufficient Funds – Not enough fund to buy the proposed product for their school’s library system. This problem is commonly caused by lack of financial preparation for the upgrade of their school’s library system.
Operating Systems –Variation in operating system affects the effectiveness of our system. If the school’s operating system is not compatible the proposed program will not operate or function well.
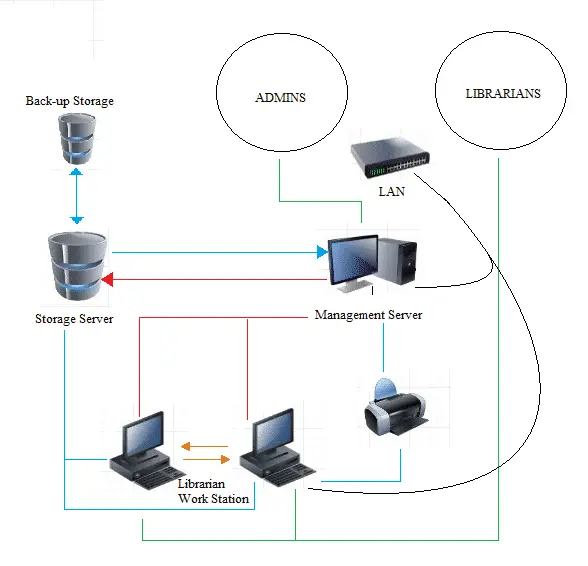
Architectural Diagram Interface of Hardware
The diagram shows the management server. This is where all the process starts. It shows that it delivers and retrieves data from the storage servers and is distributed to the librarian workstations.
Management server is also responsible for passing up the database to back-up storage to secure a copy of all registered book and students in the system including their borrowing and return book transactions.
System Testing and Implementation
In order to make this project successful, the researchers let the proponents test and evaluate SCA Library Management System in order to receive feedbacks and to produce a reliable and effective system.
SCA Library Borrowing System was tested in the school laboratory by the proponents. Firstly, the selected student will login as an administrator to see and evaluate the functions of administrator in the system. Secondly, the researchers let the two students to login as Librarian to evaluate the functions made for the librarian’s point of view in the system.
SCA Library Borrowing System is a customized system which is designed from the client’s desire in the system to make it more user friendly to the target users. The items below are the features included in the system.
SCA Library Borrowing System Features
This SCA Library Borrowing System will feature the following:
- Computerized Admin / Librarian / Student Account Managements
- Secure storage for accounts and transactions
- Easy book borrowing schemes
- Generating well-organized reports
Recommended Hardware Specification (Server / Work Stations)
For SCA’s Library Management System be deployed and run in a perfect functions the clients must first implement the following hardware specifications.
- Intel Core i3-2100 3.10GHz
- 8GB 1333MHz DDr3
- Printer
- Optical Mouse
- Keyboard
- Monitor
Recommended Software Specification (Server / Work Stations)
- Windows 7 Ultimate / Professional
- Visual Basic 2008
- PHP, MySQL
- MySQL Database and MySQL utilities
- Crystal Report
Recommended Network Specification
- Dual 1 GB LAN ports
- UTP cables
- RJ45
Conclusion
This Chapter 3 Methodology is for students in order for them to have an idea on what to write in their own Chapter 3 Methodology.
Here are Chapters 1 and 2 of the Library Borrowing System Documentation:
- Library Borrowing System Documentation | Chapter 1 – Introduction
- Library Borrowing System Documentation | Chapter 2 – Review of Related Literature
Related Capstone Resources
- Chapter 3 Methodology Attendance Monitoring System 2019 Doc
- Enrollment System Thesis Documentation Chapter 3
- Chapter 3 Online Restaurant Management System Project Documentation
- Crane Thesis Documentation Chapter 3 Methodology
- Classroom Management System Thesis Documentation Chapter 3
- Sales And Inventory System Thesis Documentation Chapter 3