Library Borrowing System Documentation | Chapter V – Proposed System
Chapter 5 – Proposed System will discuss your proposed system and describe it using different diagrams. This will show that you have achieved your objective from the first chapter.
Here is the guide of the content for Chapter 5 – Proposed System.
How to write Chapter 5 – Proposed System
- Proposed Solution
- Scope of the Study
- Concept of Operation
- Use Case Description
- Data Flow Diagram
- Data Dictionary
- Class Diagram
- Entity Relationship Diagram
- Advantages and Disadvantages of the Proposed System
- Technical Feasibility
- Social and Operational Feasibility
- Economic Feasibility
Proposed Solution
Throughout the research, the researchers came up and decided to propose a quick and easy transaction for all the manual difficulties in managing the Library have been rectified by implementing computerization to make it faster and reliable managing system, the researchers will also provide a user-friendly interface for the librarian and administrator and also a fast accessible database with a secure and huge amount of storage capacity. It will also provide a fast phased of technology attributed a lot to the improvement of the library system.
Scope of the Study
The proposed system is made based on the wants and needs of the school, the system consist of registering books with specific book identification number, so that the librarian will have an easy access in each book, search tabs for reliable, easy and faster monitoring of books and more importantly a reports and evaluation papers can be generated in a well-organized and well-presented reports.
In this project the system is highly recommended due to the rapid increase of computer related tools in the industry. With this proposed system features and functions the school library will be able to accommodate more reliably consistent and faster to provide a better service to the students.
The SCA’s library borrowing system starts with the registered administrator’s account which was made by the system programmer and is given to the supposed administrators of the system when the system is activated, the administrator will add users to the system which is the librarian, when librarian is registered he/she can now manage and record books in the system.
He/she can register students who enrolled in the school. If a student, who is registered in the system, wants to borrow a book, he can inquire with the librarian if the book is available or is already borrowed by other student.
The moment that it is available he must search the book in the library shelf and present the book with his registered library ID, the librarian will encode the book and student ID number in the system and when it is encoded the system it will automatically record the book and student details in the database.
Concept of Operation
In the second main transaction, when the student will return the book, the librarian will search the borrowing transaction records, when the record is found, there will be three (3) outcomes.
First, when book is returned in a good condition and is not late there will be no penalties to be released. Secondly, loss of book or damaged, the librarian will release a penalty report which will be forwarded to the accounting office through a printed-out report.
Lastly, when the book is returned late, the librarian will sum-up the total number of days. There will be a fine of 20php per day and will also be forwarded to the accounting office in the same manner.
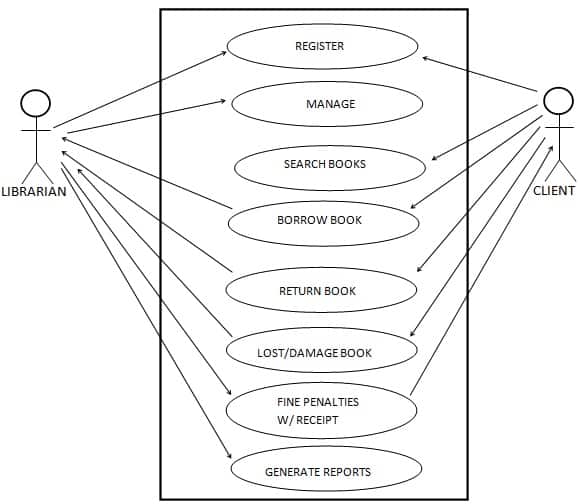
The main actors as shown in Figure 5, Proposed SCA Library Borrowing System Use Case Diagram are Client, Librarian.
The corresponding use cases for the Client are, Inquiry for Membership, Search Book, Borrow Book, Book Return, Pay Fine and for the are Librarian, Search Book, Issue Membership Card, Issue Book, Return Book, Charge Fine In Case of Late Return, damage or the book is lost; maintain the Book Records, Add Books, Remove Books, Add Members, Remove Members, and Update Member. Also generating report for client and school needs.
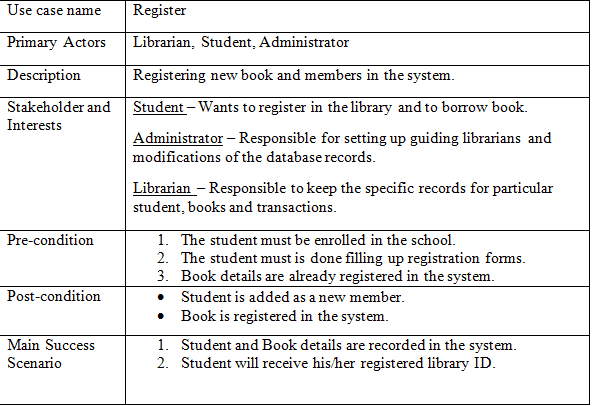
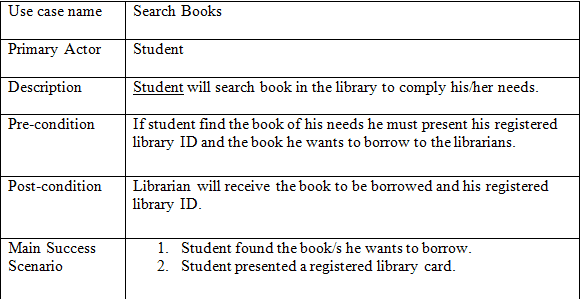
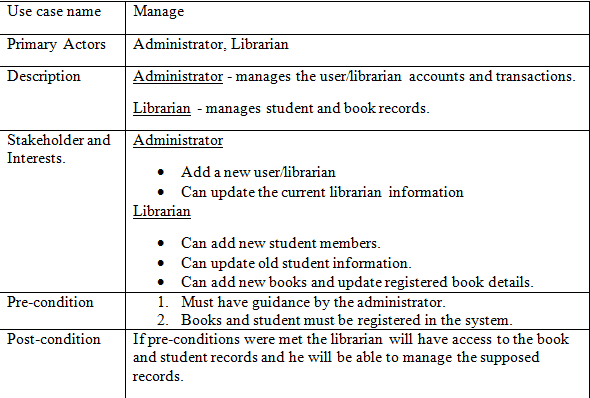
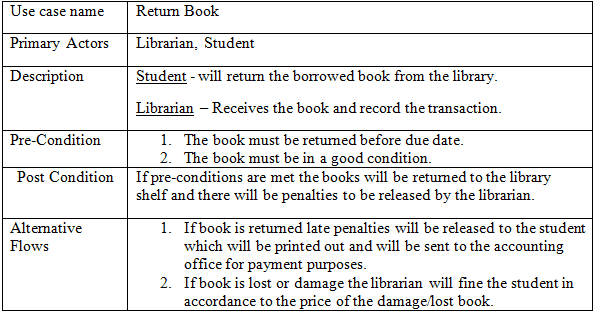
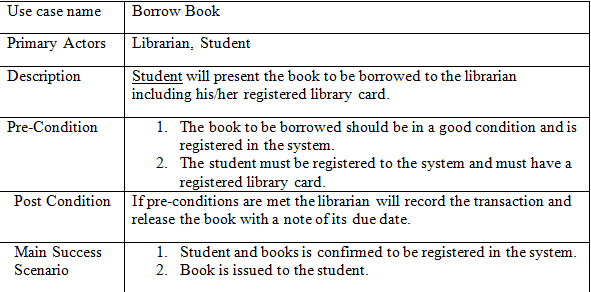
Use Case Description
The table below describes the functions, conditions and alternative flows to be met of all the entities used in the use case diagram.
Data Flow Diagram
In figure 6 of the proposed system’s Data Flow Diagram shows all the concept and flows of each entities and operation of the proposed system.
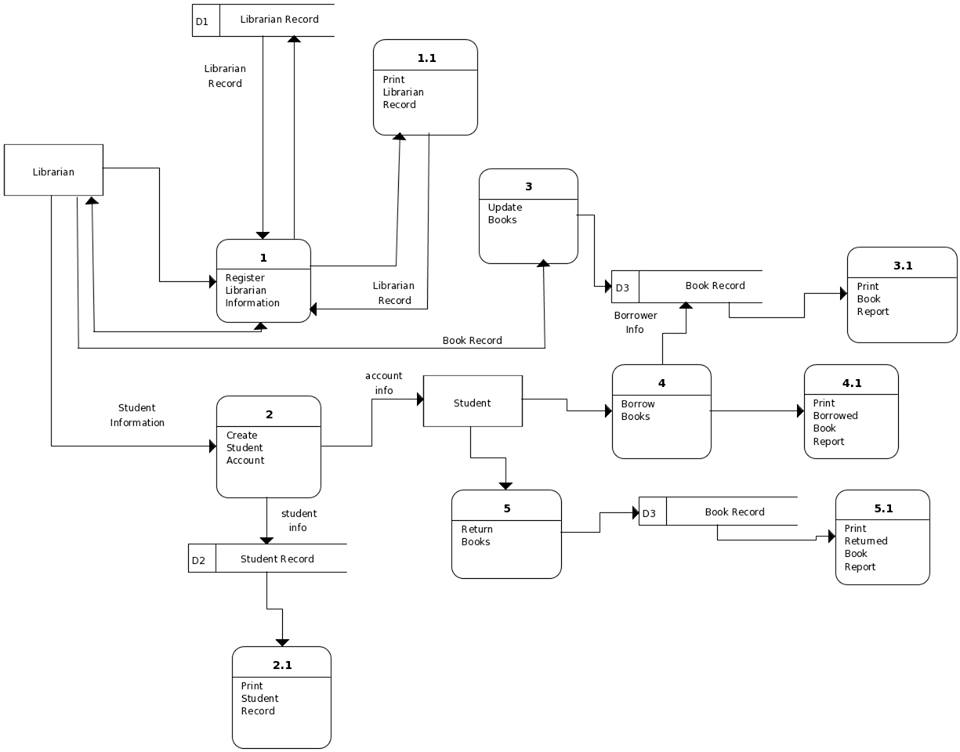
The librarian will log in to the system and then the librarian will register students and books that are in the library. If the students have been registered and wanted to borrow books, the student will search the book/s, and then he/she will present his/her registered library card together with the book/s he/she intended to borrow.
The librarian will record the transaction using the proposed system and will set the due date for the book to be returned. After recording he/she will release the book/s and student’s library card together with the receipt.
When the student returned the book before the due date, the staff will record the transaction successfully and update the book status. In case of loss or damaged, the librarian will give a fine to the student that will be given to the accounting office for penalty purposes.
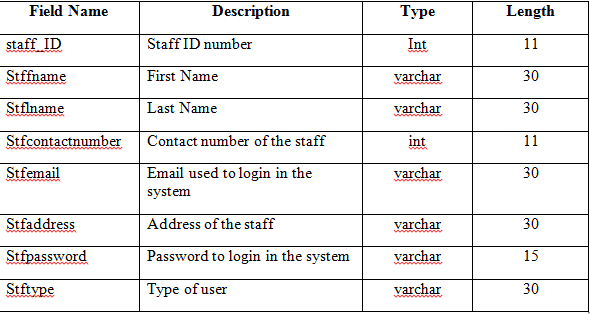
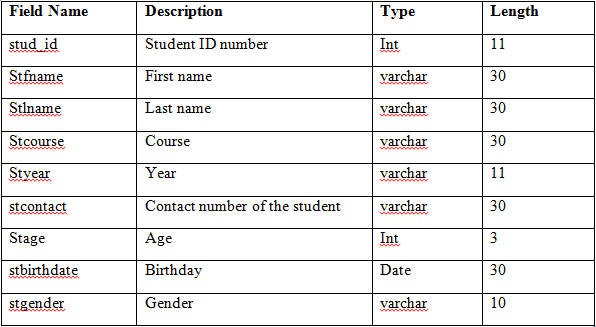
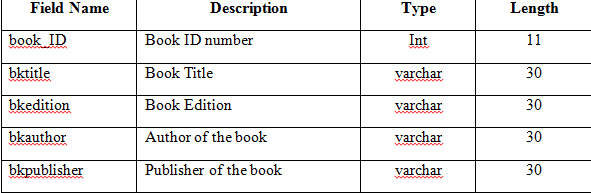
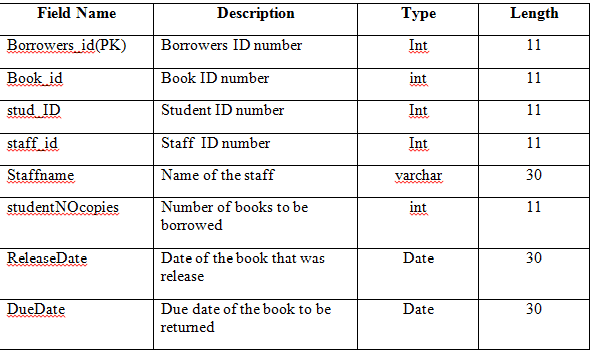
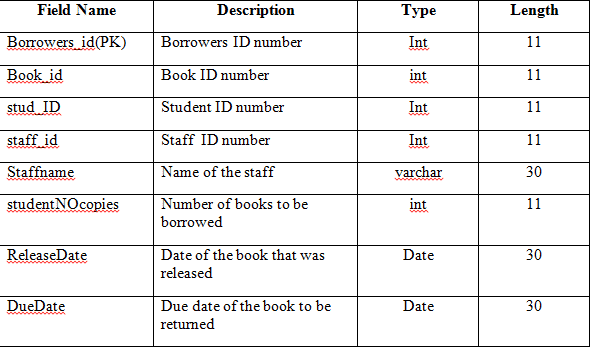
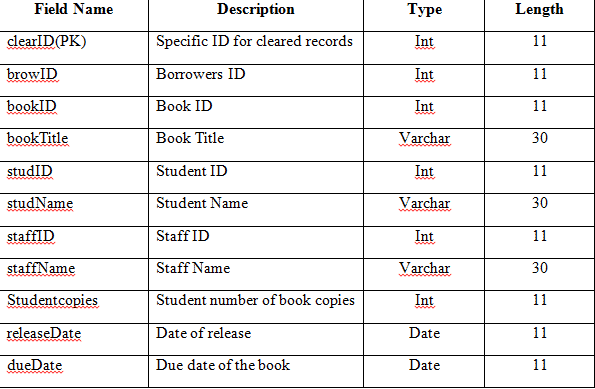
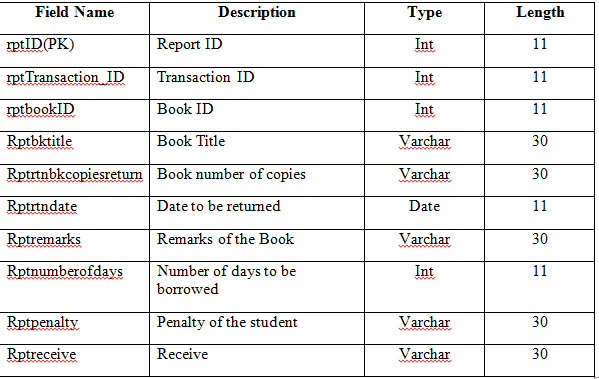
Data Dictionaries
These tables below provide the entire database tables details such as Field Name, Descriptions, data types, character lengths.
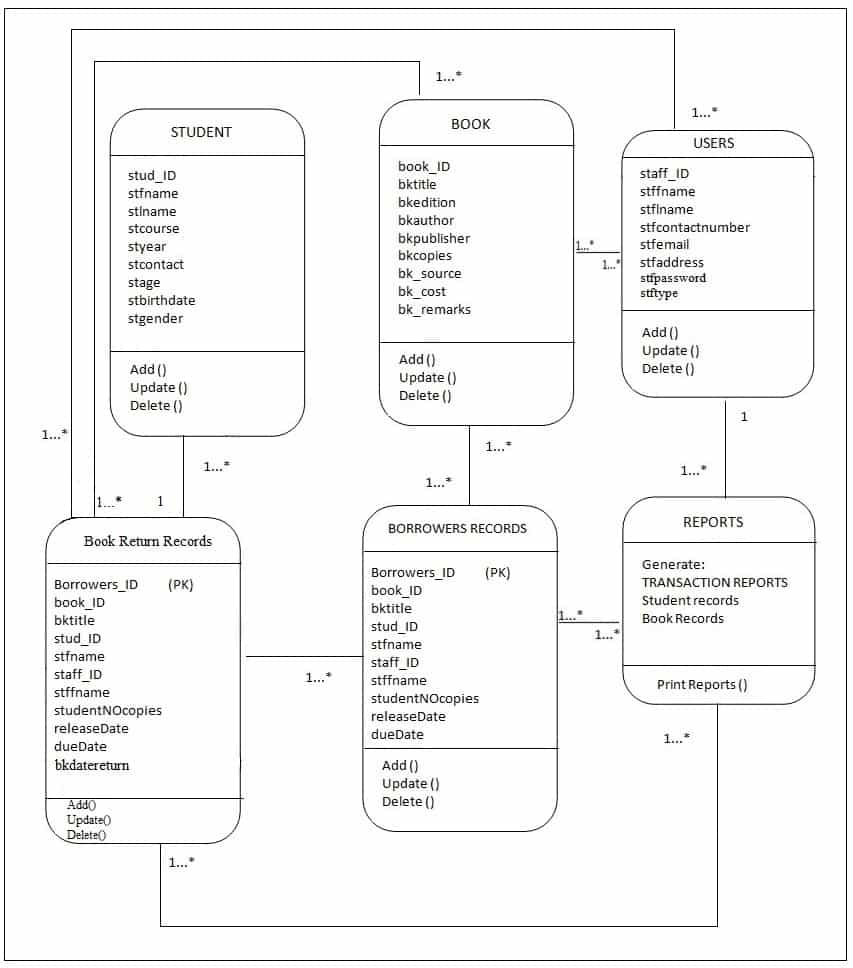
Class Diagram
Figure 7 Proposed SCA Library Borrowing System Class Diagram shows the system entity, attribute and operations and each relationship among objects.
Entity Relationship Diagram
Figure 8 Proposed SCA Library Borrowing System Entity Relationship Diagram shows the system entity relationships in each entity and their supposed functions in each relationship.
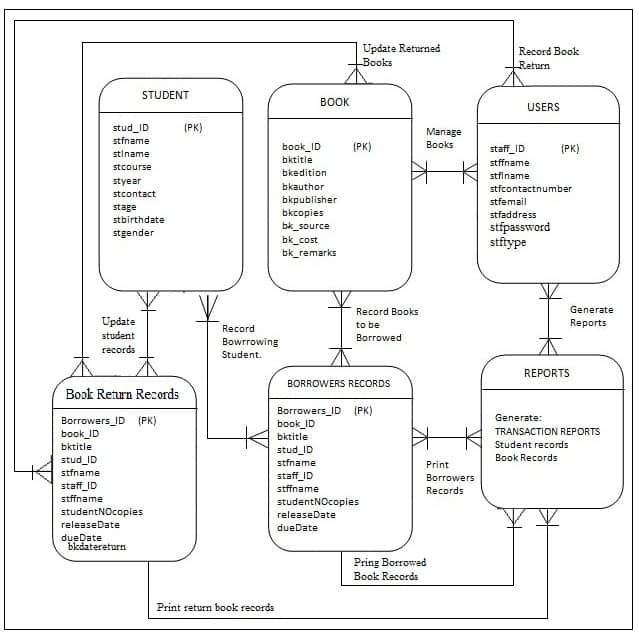
Based on figure 8, the proposed system’s Entity Relationship Diagram are the entity of the proposed SCA library borrowing system database, which are presented by tables; the tables are made to meet the required specification of the system and provide a much more specific details of the each entities within the system.
Advantages
The following are the advantages of our system:
- Provides quality and time sufficient services.
- User friendly and easy to use.
- Provides specific reports.
- Reliable and easy to manage records
Disadvantages
The following are the disadvantages of our system:
- One (1) book per transaction only.
No password recovery
Technical Feasibility
During the study, the researchers concluded that this study is technically feasible because there will be no much trouble and difficulty in getting the required resources for the development and maintenance of the system. As well as all the resources for software and hardware development is already available.
Social and Operational Feasibility
The proposed library borrowing system study is socially and operationally feasible for the organization because the system is developed with the organization’s wants and needs in order to easily understand and manipulate the systems functions, so the researchers and developers made sure that the system will be user friendly and can be easily operated to meet its fully operational function to provide the organization a social and operational system.
Economic Feasibility
In the development of the proposed system the researchers concluded that this study is highly and economically feasible because the organization will not spend large amount of money in order for the system to be developed and be fully functional.
The only consideration left to do is to make an environment that is capable to attain the maximum usability of the corresponding resources.
Conclusion
This Chapter 5 – Proposed System of Library Borrowing System is free to use as basis for student thesis. Surely, this guide will help you finish your own Library Borrowing System documentation.
Feel free to leave your suggestions and comments down below. For other articles:
- Library Borrowing System Documentation | Chapter 1
- Library Borrowing System Documentation | Chapter 2
- Library Borrowing System Documentation | Chapter 3
- Library Borrowing System Documentation | Chapter 4
- Attendance Monitoring System Documentation | Chapter 1
- Attendance Monitoring System Documentation | Chapter 2
- Attendance Monitoring System Documentation | Chapter 3
- Attendance Monitoring System Documentation | Chapter 4
- Attendance Monitoring System Documentation | Chapter 5